Sir Francis Bacon was an extremely important
politician at the court of King James I, and thus was no stranger to intrigue.
In the course of his day job, he was necessarily involved in the world of
espionage and spies and which, unless you’ve been involved in it, you’d imagine
being all cool and so forth but if you have been involved in that world then
you will know it to be dull, boring and mind-numbingly tedious. Bacon knew a
lot about codes, ciphers and cryptography; he wrote quite a bit about them in his
numerous works. Book Six of The Advancement of Learning is where
he explains the system of cryptography that is called a bi-literal cipher.
 |
| Francis Bacon - Frontispiece - Novum Organum |
It
works like this. At its heart, it’s a substitution cipher, which means that one
thing stands for something else. The simplest sort of this sort of cipher is
when a single letter stands for another letter; this is called a Caesar
Cipher or a shift cipher. For instance, let’s say we substitute each
letter of the alphabet with the letter that follows it in the alphabet – so the
word ‘cat’ would be rendered as ‘dbu’, or ‘dog’ would be
rendered as ‘eph’.
Bacon starts by taking this a step further, whereby
five letters are substituted a single one. The letter ‘a’ becomes ‘aaaaa’. The
letter ‘b’ becomes ‘aaaab’. The letter ‘c’ is ‘aaaba’. The whole of the
alphabet is rendered thus, down to ‘z’ as ‘babbb’. You can see the full alphabet in this illustration.
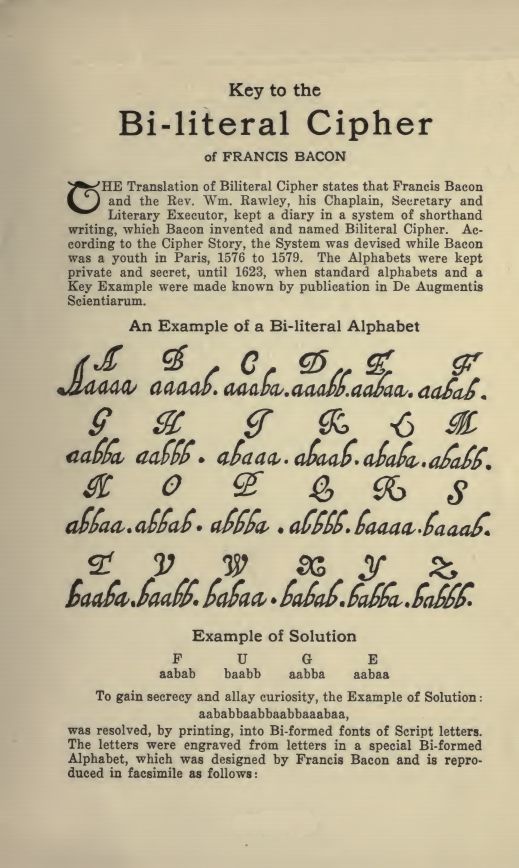 |
| Francis Bacon - Bi-Literal Cipher |
So far, so
good. The next step is to take the five letter substitutions for the letters of
the message you wish to encrypt. Let’s say, for example, we need to send the
warning ‘Fly’ to an agent. We take the three five-letter sets for the
individual letters of our message - the letter ‘f’ is ‘aabab’, the letter ‘l’
is ‘ababa’ and the letter ‘y’ is ‘babba’. So, we now have ‘aabab ababa babba’.
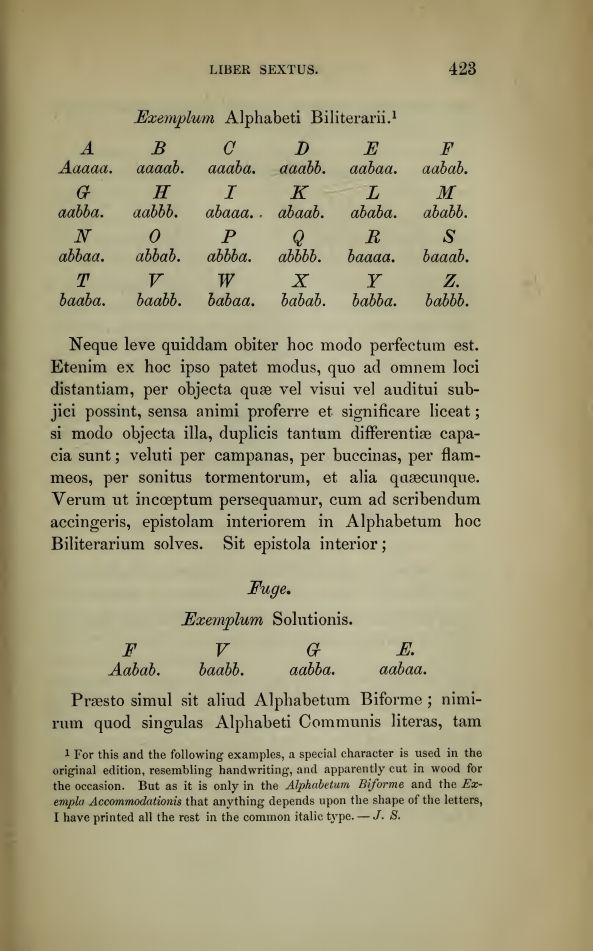 |
| Francis Bacon - De Augmentis - Book 6 - Bi-Literal Cipher |
We now need a seemingly innocent phrase that will not arouse suspicion. It
doesn’t what this is, providing it contains at least the same number of letters
as our little coded substitution (in this case, at least fifteen letters). Let’s
use the phrase ‘Stay where you are’, (which just happens to have fifteen
letters in it). Now take the coded letters and write the phrase beneath it,
thus:
aabab ababa babbastayw herey ouare
and then, wherever there is a letter ‘a’ write a
normal, roman letter but where there is letter ‘b’, write an italic letter
instead. This gives us:
aabab ababa
babba
stayw herey ouare
And there you have your encrypted message, when you
move the letters back into their proper order. It now reads:
Stay where
you are.
Now, to decode it, our hypothetical agent splits our
message into groups of five letters, and for each ‘normal’ letter he writes an
‘a’ and for each italic letter, he writes a ‘b’, and then looks at his alphabet
and matches the relevant block of five ‘a’s or ‘b’s with its corresponding
letter, thus giving him the letters of the true message, and he takes the
appropriate action (we hope).
In the above example, to make the difference a
little easier to see, I’ve used bold and italic letters. But to send a less
conspicuous message, it would be better to use two distinct fonts – let’s call
them font-a and font-b. The letterforms are similar enough not to arouse
suspicion but different enough to allow them to be used in the code.
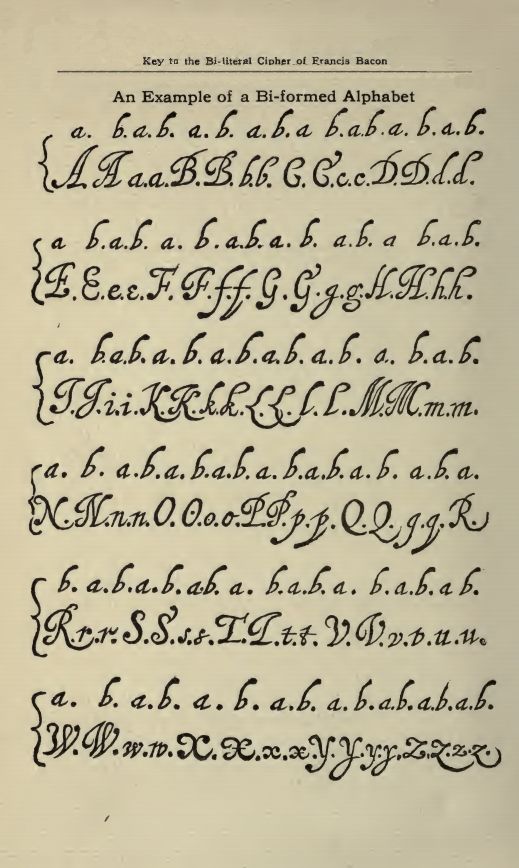 |
| Example of a Bi-Literal Alphabet |
You can
see in the illustration, for example, that the two capital letter ‘A’s are
similar, but the font-a capital letter is a little plainer than the font-b
capital, which has a flourish at the top and slightly curlier serifs at the
bottom. It is the same with each letter; each is just that tiny bit different
in the font-a and font-b examples. Bacon uses the following example to make his
cipher clear. He takes a message sent from a Spartan general that reads,
“Perditae res. Mindarus cecidit. Milites Esuriunt. Neque hinc nos extricare, neque hic diutius manere possumus.” (It means, basically, that All is lost, Mindarus is killed, the soldiers are hungry and we can neither escape nor remain here).
Then, taking the words one by one, letter by letter, they are coded into their
five letter counterparts. So, in the first word, ‘Perditae’, P = abbba, E =
aabaa, R = baaaa, D = aaabb, I = abaaa, T = baaba, A = aaaaa and E = aabaa.
This is done for each of the words.
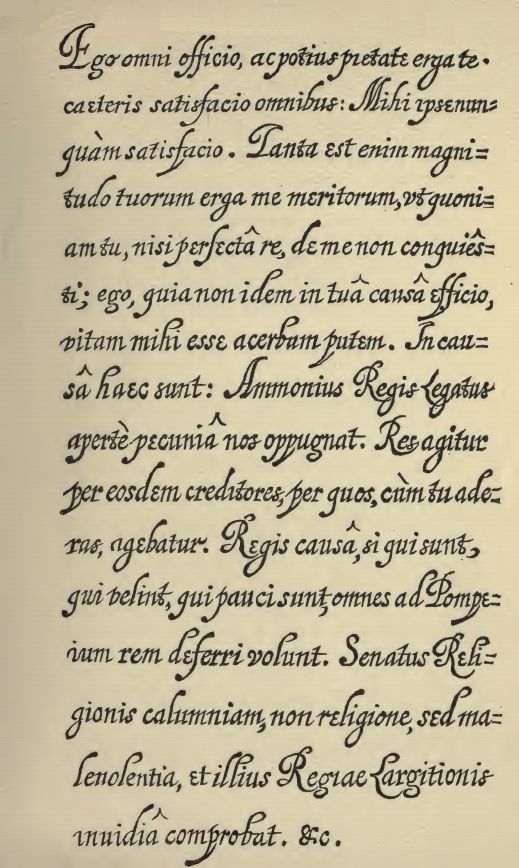
When this is done, Bacon selects another
text that will serve as the innocent message that will convey the code. He
chose one of Cicero’s Epistles that begins, “Ego omni officio.” Where
each letter in his coded message corresponds to an ‘a’, this is set using
font-a. Where there is a ‘b’, then font-b is used – so for the first letter of
‘Perditae’, the letter P, which is encoded as abbba, he uses font-a, font-b,
font-b, font-b, font-a. Slowly, the whole message is encoded using the two
different fonts. The result can be seen in this illustration.
 |
| Bacon's Coded message using his Bi-Literal Cipher in an Epistle of Cicero |
When the message
is received, the agent disregards what the text says on its face-value. He
simply divides the text up into blocks of five letters. So, ego omni officio
becomes egoom/nioff/icio[a], and then the font-a letters are written as ‘a’ and
font-b letters are written as ‘b’. This gives abbba aabaa baaaa – the PER at
the beginning of Perditae. And so on and so on until the whole of the
message is revealed.
It is an elegant system of coding if a little outdated and
impractical in today’s world, where different fonts are far too conspicuous in
emails and other electronic texts. However, the nuts and bolts of Bacon’s
bi-literal system work on the difference inherent in a binary system, which is
ideal for use in the on/off binary world of computers. (Remember, there are 10
kinds of people in this world – those that understand binary notation and those
that don’t).
No comments:
Post a Comment